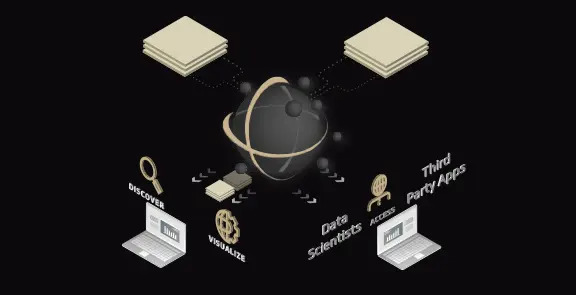
Knowledge Is Power, Leverage All of Your Data
AMP enables users to intuitively interact with and analyze enterprise data. AMP exposes textual, temporal, and spatial search parameters for ALL of your holdings.

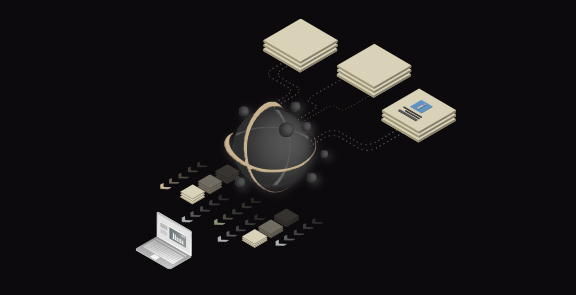
Data First
AMP provides cataloging and content management services for data types such as IMAGERY, ELEVATION, VIDEO, VECTOR, EVENT DATA, and TEXT.
Imagery
Single-band, multi-spectral, airborne, thematic, commercial, or private images; AMP crawls tags, manages, and makes your enterprise data discoverable through massively parallel workflows to users of all experience levels.
Elevation
Point to pixel – LiDAR processing pipelines bring life back to your historic LiDAR collection, allowing you to efficiently expose new collections and incorporate them as part of your enterprise’s 3D capabilities.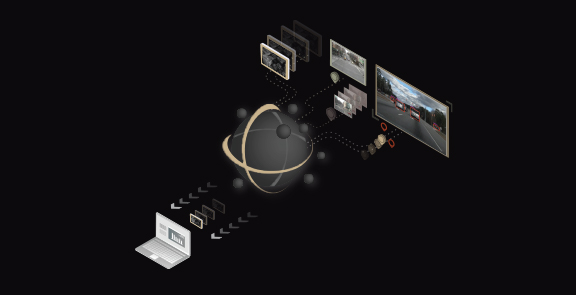
Video
Full-motion video, airborne, static surveillance, and special reconnaissance capabilities are all handled by AMP. We simplify the discovery of historic video and bring it to your users’ fingertips.
Vector
Vector data includes OpenStreetMap data; and common GIS formats such as Shapefiles, Geodatabases, and KMLs.
Event Data
Location intelligence content, or high-cadence spatio-temporal datasets, are now discoverable within AMP. Process these highly resolute datasets, exposing them for retrieval while enabling scalable discovery and analytics, providing users with an immersive understanding of their data.
Text
Text files sitting on a share? No data management plan in place? What are your data gaps? AMP crawls, enriches, indexes, and exposes your organization’s unstructured text for end-user discovery.Immersive Experiences
AMP catalogs content so that users can aggregate and visualize millions of datasets while providing the granularity and specificity of a digital asset management platform.
Visualize
Need data? Leverage AMP Visualize to delve into your content. Apply geofences and filter datasets by space and time. All of your data can be accessed and viewed within AMP Visualize. Find the right data you need, and analyze it using AMP native tools or the analytical tool of your choice.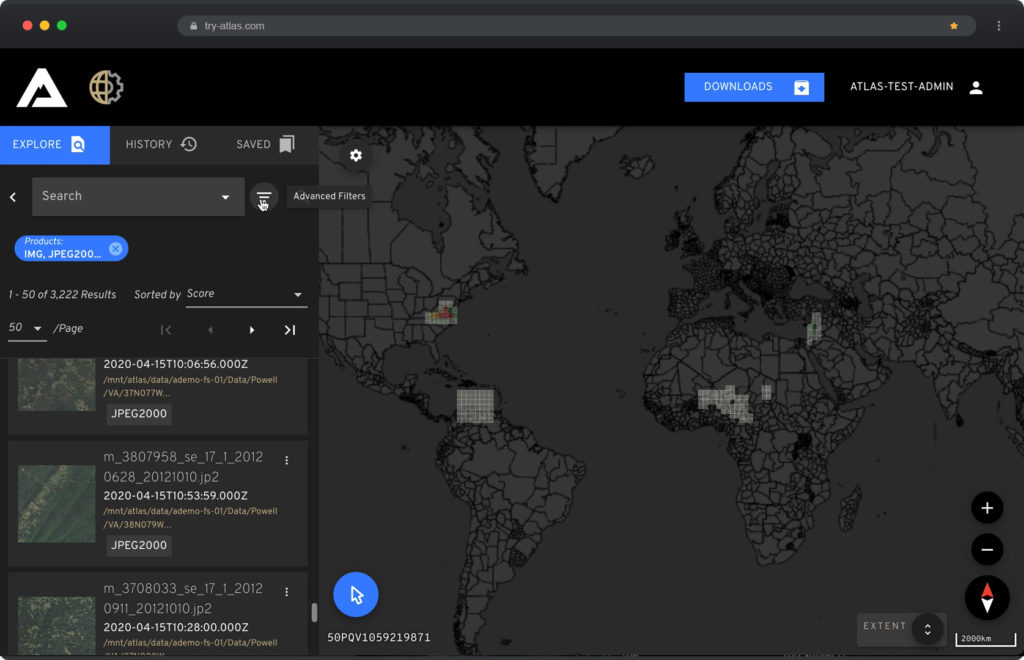
Discover
The AMP Discover search interface allows users to contextually and temporally find information relevant to their end objectives. Discover documents, populate advanced searches, and filter and tag video content within our focused search interface.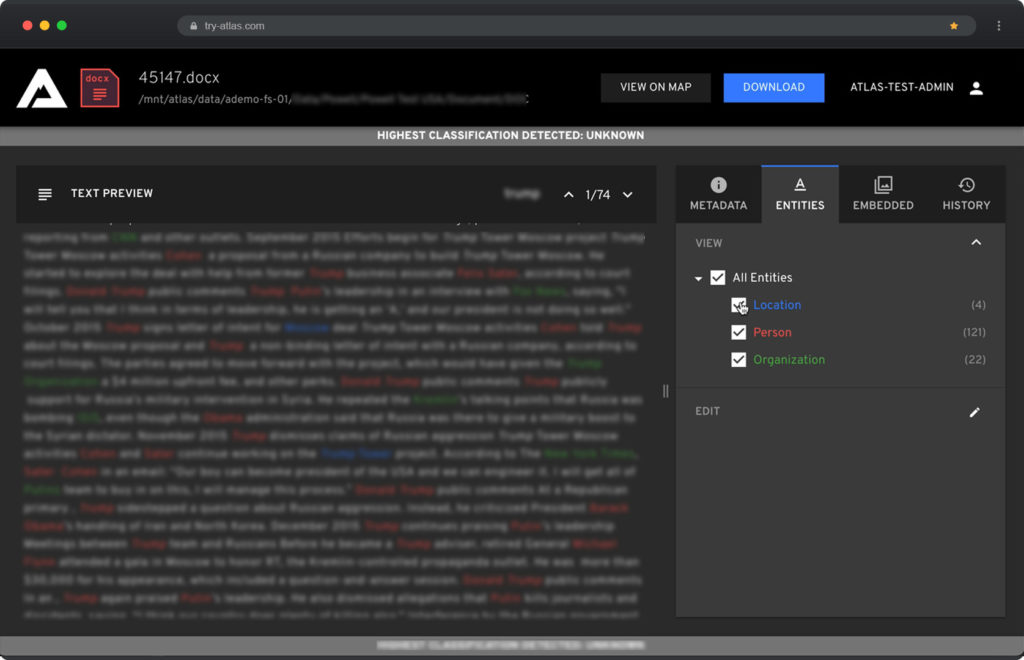
Manage
The AMP Manage user interface is your ecosystem’s data processing and task monitoring hub. With AMP Manage, administrators can invoke new processing tasks, monitor user activity, and schedule jobs for completion during network downtime.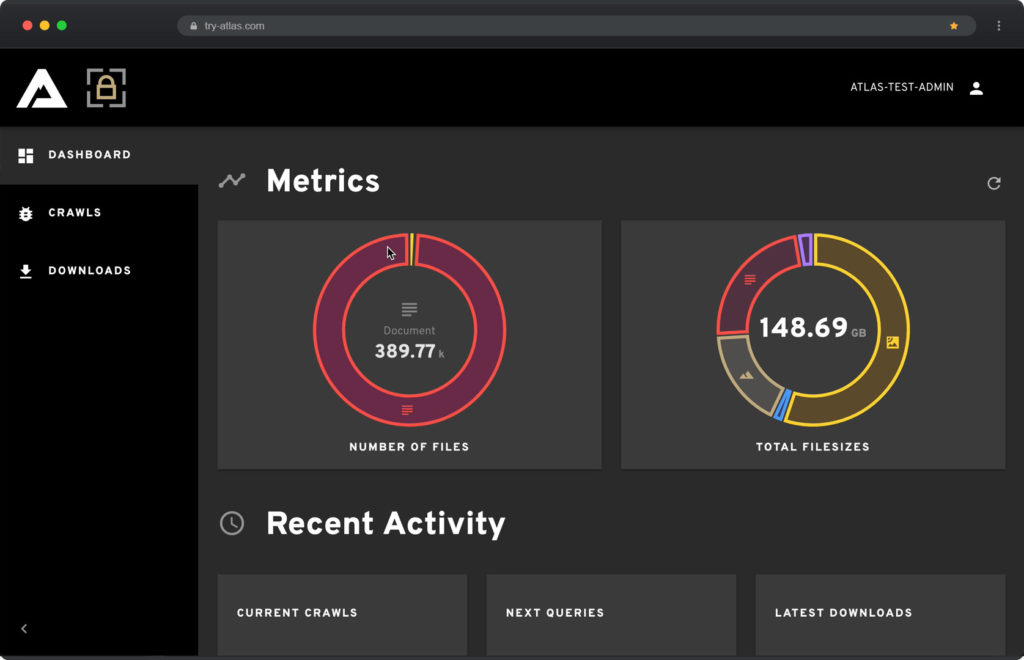
Unencumbered Access
AMP yields a well-documented API; users can migrate content rapidly for short-notice
deployments or even search different ATLAS instances remotely. Integrate with legacy applications.
Provision
Remote data access is a tried-and-true challenge for expeditionary analysts. AMP intelligently catalogs your data holdings so that you can access them on demand or subscribe to pertinent content as it comes online.
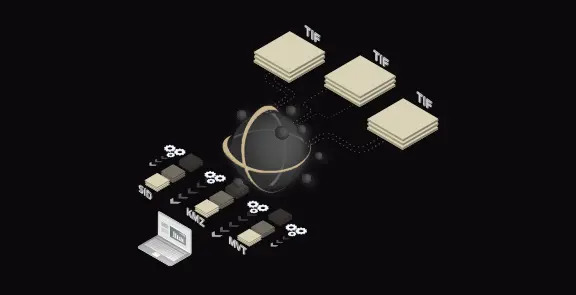
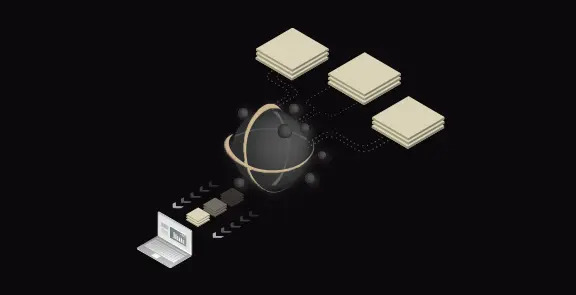
Transform
Not all applications are created equal. AMP is your tactical Rosetta Stone. Flex the ecosystem to transform, compress, and condition your content for use in your finishing tool of choice.
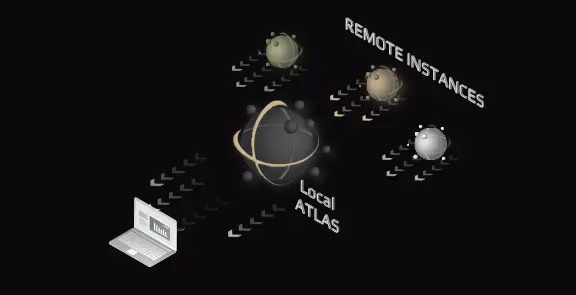
Federate
So you traveled to a remote environment? What good are global data holdings if your network won’t support streaming on demand? AMP allows you to search your local holdings, as well as plug into remote AMP instances. Now you can get what you need when you need it.
Integrate
AMP feeds its web applications and interoperability with third-party applications via the ACCESS API layer, creating a seamless data experience for users and conducting a variety of tasks within any application.
AMP Users
deployed person, you can leverage ATLAS to find your mission data when you need it.
Analysts on-the-go
Search, select, and quantify your data, and then bring it with you with AMP. Your days wasting time using inefficient and tedious data management pipelines are over. Spend your time delivering pertinent insights and reflections to those who need it. Conveniently package subsets of data for use on your portable devices.
Data wranglers
AMP is built on top of a world-class data management ecosystem. It simplifies the authoring of data management pipelines, extending pertinent enterprise content to users, analysts, and app developers.
Scientists and Data Ninjas
HOW CAN WE HELP?
We’re committed to securing your data, from intellectual property and trade secrets to
software architecture and personal identifying information.
Trusted By Many